PseudoManuscrypt Malware: High-Volume Espionage and Industrial Infiltration
- APRIL 27TH, 2026
- 2min read

While many malware campaigns focus on quick financial theft, PseudoManuscrypt represents a more harmful breed of threat: the professional spy. First identified for its massive scale and complex code, this malware is designed for deep-level espionage. It doesn’t just steal a credit card number; it steals blueprints, research data, and engineering secrets. In the world of PseudoManuscrypt, your organisation’s intellectual property is the primary currency.
What is the Attack?
PseudoManuscrypt is unique because it combines the complexity of a Nation-State Advanced Persistent Threat (APT) with the distribution methods of common malware.
1. The Malicious Installer: Attackers bundle the malware with pirated versions of high-end professional software, such as CAD tools, specialised engineering utilities, or common office suites.
2. The Multi-Stage Payload: Once the “cracked” software is installed, PseudoManuscrypt unfolds in stages. It checks for the presence of antivirus software and attempts to disable security tools before downloading its various spying modules.
3. Persistence: It embeds itself deep within the Windows registry and system startup processes, ensuring that even if the pirated software is deleted, the spy remains active.
Securing Your Organisation
1. System Update: Patch and update all systems, especially Windows and Industrial Control Systems software, disable unnecessary services and enforce least-privilege access.
2. Avoid downloading cracked or pirated software: verify download sources and use official software channels.
3. Training: Educate users on phishing and the dangers of malicious software through regular awareness training.
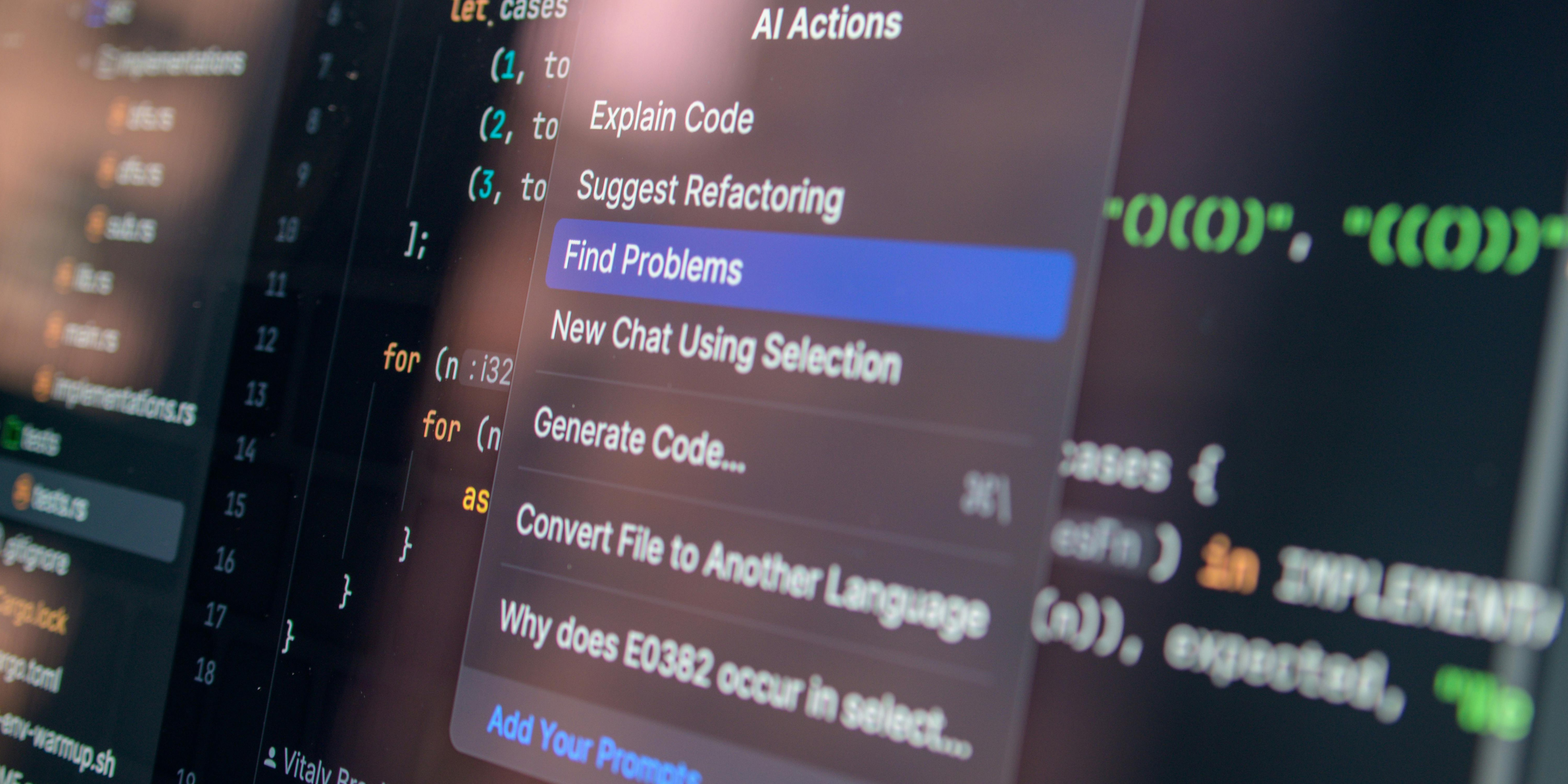
4. Implement EDR Tools: such as TrendMicro, to detect anomalous behaviours like unusual command and control (C2) traffic. Segment Industrial Control System networks and monitor for persistence artefacts in registry hives.
Explore more CIL Advisories
Continuous Penetration Testing: Closing the Vulnerability Gap with Autonomous AI
For years, organisations have relied on periodic, manual penetration testing to secure their most critical applications. However, due to time…
APRIL 20TH, 2026
Read More
Hardening OT/IT Convergence Against State-Sponsored Threats
The historical "air gap" between Operational Technology (OT) and Information Technology (IT) has effectively vanished. In the drive for "Industry…
APRIL 17TH, 2026
Read More
Mitigation of Supply Chain “Poisoning” & Open Source Software (OSS) Risk
Modern software development relies heavily on open-source components; roughly 80-90% of a modern application's code is not written by its…
APRIL 14TH, 2026
Read MoreNever miss a CIL Security Advisory
Stay informed with the latest security updates and insights from CIL.


