Continuous Penetration Testing: Closing the Vulnerability Gap with Autonomous AI
- APRIL 20TH, 2026
- 2min read
For years, organisations have relied on periodic, manual penetration testing to secure their most critical applications. However, due to time and cost limitations, these tests are often conducted only once or twice a year, leaving the majority of an application portfolio exposed in the periods between tests. Furthermore, traditional Static and Dynamic Application Security Testing (SAST/DAST) tools often generate isolated alerts without understanding how a low-severity bug can lead to a critical breach.
The catastrophic danger of uncontextualized, chained vulnerabilities was demonstrated globally during the 2021 Microsoft Exchange “ProxyLogon” attacks. Threat actors successfully chained four separate zero-day vulnerabilities together. They started with a Server-Side Request Forgery (SSRF) to bypass authentication, which then allowed them to exploit file-write vulnerabilities and achieve full Remote Code Execution (RCE). Traditional scanners failed to connect these isolated flaws, resulting in the compromise of over 30,000 organisations worldwide before manual testing and patching could catch up.
Best Practices & Mitigation Strategies
To close the vulnerability gap, continuous, AI-driven validation must replace periodic manual penetration testing to test your entire infrastructure in hours, not weeks.
Deploy Autonomous Penetration Testing
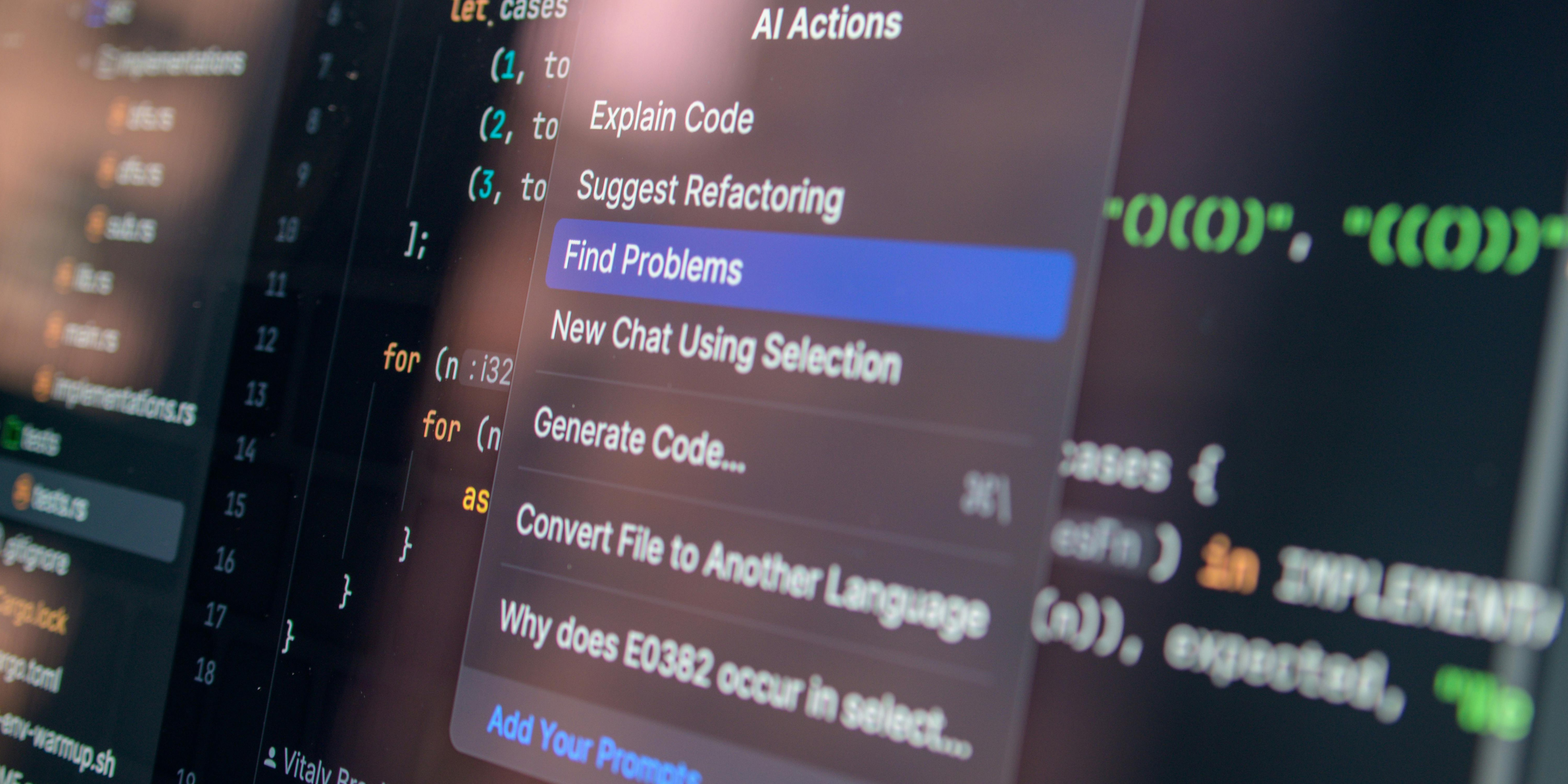
Utilise frontier AI tools, such as the newly released AWS Security Agent, to run on-demand, 24/7 penetration tests. These autonomous systems scale massively, actively identifying potential vulnerabilities and attempting to exploit them with targeted payloads to confirm they are legitimate risks.
Implement Context-Aware Security
Move beyond blind scanning. Feed your security agents rich context—including architecture diagrams, infrastructure-as-code, and threat models. This allows the testing agent to understand how the application was designed and to identify endpoints that function “as designed” but are fatally flawed when abused by a hijacked session.
Focus on Vulnerability Chaining
Shift your remediation focus from isolated CVSS scores to validated attack chains. Ensure your testing methodology can prove how a low-priority finding can be weaponised into a critical data exfiltration event.
Test Across the Entire Portfolio
Leverage the cost-efficiency of autonomous agents to expand penetration testing coverage beyond your top critical applications to your entire multicloud (AWS, Azure, GCP) and on-premises infrastructure.
Automate the Remediation Lifecycle
Integrate on-demand testing directly into your CI/CD pipeline. When an autonomous agent validates an exploit, it uses its insights to automatically generate pull requests with code fixes, enabling developers to merge solutions in hours rather than weeks.
In modern software development, development velocity cannot outpace security validation. By adopting autonomous, context-aware penetration testing, you eliminate the waiting periods of manual testing, reduce false positives, and ensure that every application you deploy is actively hardened against sophisticated, chained attacks.
Explore more CIL Advisories

PseudoManuscrypt Malware: High-Volume Espionage and Industrial Infiltration
While many malware campaigns focus on quick financial theft, PseudoManuscrypt represents a more harmful breed of threat: the professional spy.…
APRIL 27TH, 2026
Read More
Hardening OT/IT Convergence Against State-Sponsored Threats
The historical "air gap" between Operational Technology (OT) and Information Technology (IT) has effectively vanished. In the drive for "Industry…
APRIL 17TH, 2026
Read More
Mitigation of Supply Chain “Poisoning” & Open Source Software (OSS) Risk
Modern software development relies heavily on open-source components; roughly 80-90% of a modern application's code is not written by its…
APRIL 14TH, 2026
Read MoreNever miss a CIL Security Advisory
Stay informed with the latest security updates and insights from CIL.


