Mitigation of Supply Chain “Poisoning” & Open Source Software (OSS) Risk
- APRIL 14TH, 2026
- 2min read

Modern software development relies heavily on open-source components; roughly 80-90% of a modern application’s code is not written by its developers but pulled from public repositories like NPM (JavaScript) or PyPI (Python).
Attackers have shifted focus from attacking fortified perimeters to poisoning the “water supply” — compromising these upstream libraries to inject malicious code. Traditional security tools fail here because the malware enters via a trusted update channel. The fragility of this ecosystem was starkly demonstrated in early 2024 by the XZ Utils Backdoor (CVE-2024-3094).
A threat actor spent years building trust within the open-source community to become a maintainer of the XZ compression library, eventually injecting a highly sophisticated backdoor designed to compromise SSH connections globally. This incident proved that even the most widely used, “trusted” utilities are vulnerable to human-led poisoning campaigns.
Best Practices & Mitigation Strategies
We must move from a posture of “Trust Default” to “Verify Every Component.”
Enforce Software Bill of Materials (SBOM)
You cannot secure what you cannot list. An SBOM acts as a “nutrition label” for your software. All build pipelines must generate a standard SBOM (CycloneDX or SPDX format) for every release. Deployment must be blocked if the SBOM is missing or unverified.
Software Composition Analysis (SCA) in CI/CD
Automate the detection of known vulnerabilities by integrating tools (e.g., Snyk, Sonatype, OWASP Dependency-Check) directly into the pipeline. If a critical vulnerability (CVSS > 9.0) is found in a dependency, the build must fail automatically.
Implement a “Repo Proxy” (No Direct Public Access)
Developers and build servers should never pull directly from the open internet. Configure a private artefact manager (e.g., Artifactory, Nexus) that caches approved versions and scans them before allowing them into the network. Block outbound traffic from build servers to public repositories like pypi.org or npmjs.com.
Establish Remediation Timelines
Regularly review data access logs for “large transfer” anomalies (>5GB outbound). Deploy “Canary Files” (honeypots) in sensitive folders to detect unauthorised access early, before mass exfiltration occurs.
Monitor Segmentation Coverage
Implement SCA scanning in the CI/CD pipeline immediately. Review the SBOMs of critical assets quarterly to identify and deprecate “abandonware” (libraries no longer maintained by the community). Aim for a Mean Time to Remediate (MTTR) of under 48 hours for critical vulnerabilities.
In the software supply chain, “You are what you eat.” If we build our applications on poisoned ingredients, our security is compromised before the first line of code is ever run. We must vet our software components with the same rigour we use to vet our employees and vendors.
Explore more CIL Advisories

PseudoManuscrypt Malware: High-Volume Espionage and Industrial Infiltration
While many malware campaigns focus on quick financial theft, PseudoManuscrypt represents a more harmful breed of threat: the professional spy.…
APRIL 27TH, 2026
Read More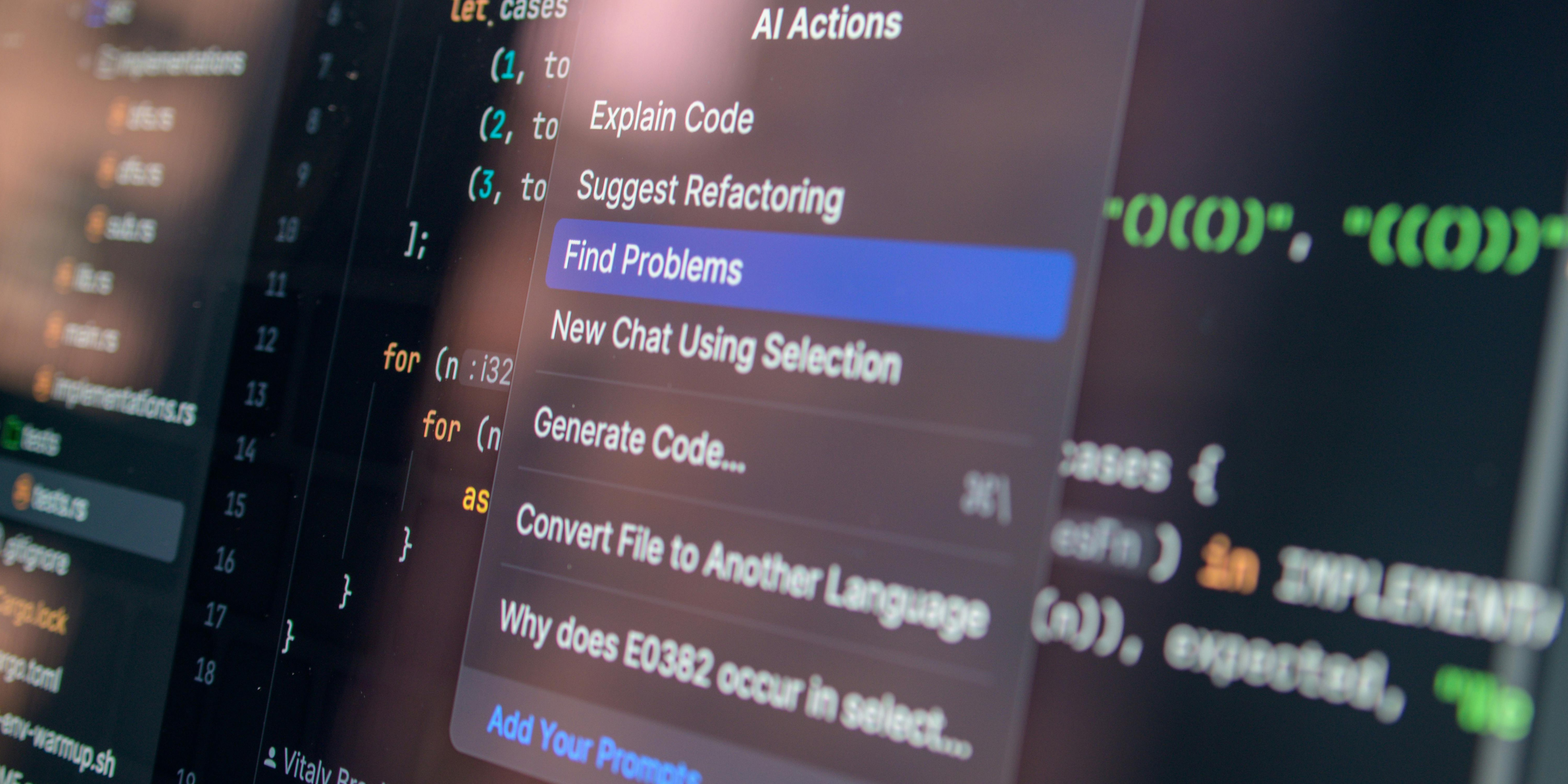
Continuous Penetration Testing: Closing the Vulnerability Gap with Autonomous AI
For years, organisations have relied on periodic, manual penetration testing to secure their most critical applications. However, due to time…
APRIL 20TH, 2026
Read More
Hardening OT/IT Convergence Against State-Sponsored Threats
The historical "air gap" between Operational Technology (OT) and Information Technology (IT) has effectively vanished. In the drive for "Industry…
APRIL 17TH, 2026
Read MoreNever miss a CIL Security Advisory
Stay informed with the latest security updates and insights from CIL.


