Phishing Emails
- DECEMBER 16TH, 2024
- 1min read
Introduction
Phishing attacks are becoming increasingly sophisticated, with malicious actors exploiting current events like the Paris 2024 Olympics Games to run phishing campaigns. Threat actors are creative and may leverage positive and negative trends.
Recently, malicious actors launched phishing emails based on the Crowdstrike incident posing as Crowdstrike technical support to lure users in order to steal their credentials, more examples here.
How to Spot a Phishing Email
- Email Address and Domain Name: Inspect emails for spelling errors. Phishing domains often mimic legitimate ones but reveal discrepancies upon close inspection. Established organisations typically own unique domains, not generic public ones.
- Body of Mail: Scammers exploit urgency to manipulate victims into opening malicious attachments, clicking harmful links, or divulging sensitive information to infect devices with malware.
- Salutation: Unexpected greetings are red flags.
- Inconsistencies: Discrepancies in email addresses, links, or domain names indicate phishing attempts.
Security Awareness Training
- Leverage our Phishing Security User Assessment and Training (PSUAT) to increase security awareness. Contact sdr@cecureintel.com for details.
Rescue the Threat from Phishing Emails
- DNS Security: Implement DKIM, DMARC, SPF, DNSSEC.
- Email Security: Use SEGs, ICES, MFA, S/MIME, PGP.
- Avoid Interaction: Do not click links/download attachments from suspicious emails.
- Report and Delete: Report suspicious emails to IT administrators, then delete them.
- Training: Empower staff with security awareness training.
Explore more CIL Advisories

Preventing Deep Fake Scams
IntroductionMalicious actors always find creative ways to defraud unsuspecting individuals; deep fake scams are one of the latest ways with…
DECEMBER 9TH, 2024
Read More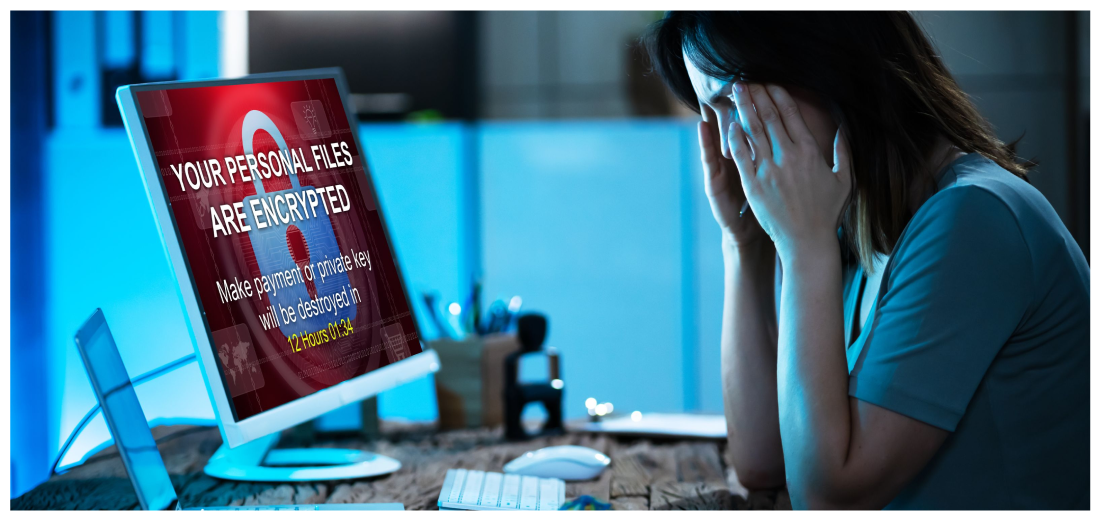
Trouble Looms: Ransomware Attacks on the Rise
IntroductionRansomware is a type of malware which prevents you from accessing your device and the data stored on it, usually…
DECEMBER 2ND, 2024
Read More
Google Chrome Zero Day Vulnerability
IntroductionWe'd like to bring to your attention a high-severity vulnerability in Google Chrome browsers and Chromium-based browsers with active ongoing…
NOVEMBER 18TH, 2024
Read MoreNever miss a CIL Security Advisory
Stay informed with the latest security updates and insights from CIL.


