Trouble Looms: Ransomware Attacks on the Rise
- DECEMBER 2ND, 2024
- 2min read
Introduction
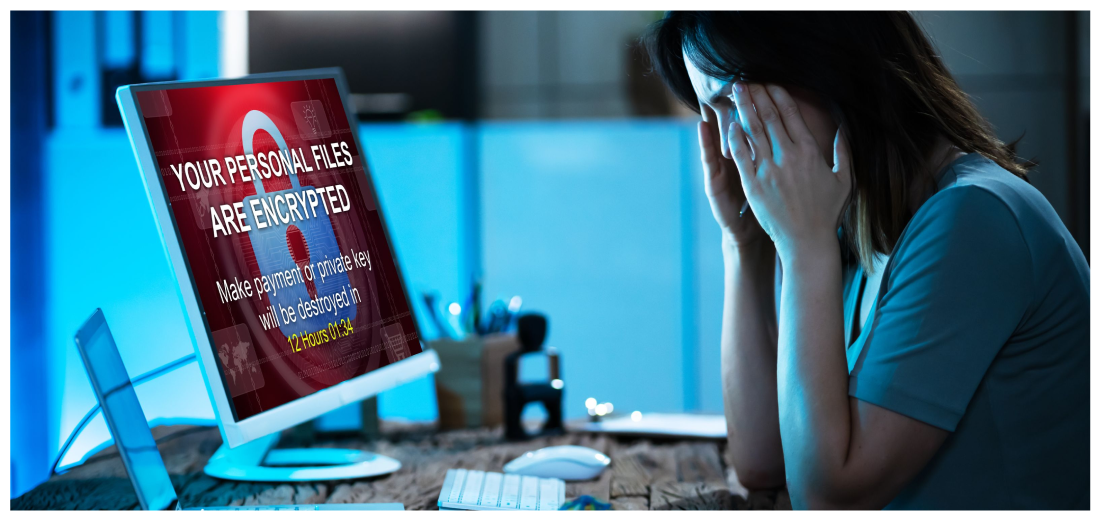
Ransomware is a type of malware which prevents you from accessing your device and the data stored on it, usually by encrypting your files. A criminal group will then demand a ransom in exchange for decryption.
There has been an increase in ransomware attacks across the world from Phobos Ransomware Group through phishing emails and RDP exploitation, and this is how it works.
Victims of ransomware attacks are advised not to engage the criminal or pay the ransom because there is no guarantee they will fulfil their end of the bargain. Systems will still be infected, and they will probably circle back. Hence, backups cannot be overestimated.
Preventing the Attack
- Limit RDP Use: Strictly limit the use of RDP and other remote desktop services. If RDP is necessary, rigorously apply best practices.
- Audit Network: Audit the network for systems using RDP and close unused RDP ports.
- Account Lockouts: Enforce account lockouts after a specified number of attempts.
- Phishing-Resistant MFA: Apply phishing-resistant multifactor authentication (MFA).
- Monitor RDP Logins: Monitor and log RDP login attempts.
- Network Segmentation: Segment the network to control traffic and restrict lateral movements.
- Encrypted Backups: Ensure backup data is encrypted, immutable, and comprehensive.
- Offline Backups: Maintain offline backups and regularly test restoration processes.
- Multiple Backups: Maintain multiple, physically separate backups of sensitive data.
- Audit Administrative Accounts: Audit administrative user accounts and enforce the principle of least privilege.
- Time-Based Access: Implement time-based access for high-level accounts.
- Disable Unnecessary Activities: Disable unnecessary command line and scripting activities.
Explore more CIL Advisories
Phishing Emails
IntroductionPhishing attacks are becoming increasingly sophisticated, with malicious actors exploiting current events like the Paris 2024 Olympics Games to run…
DECEMBER 16TH, 2024
Read More
Preventing Deep Fake Scams
IntroductionMalicious actors always find creative ways to defraud unsuspecting individuals; deep fake scams are one of the latest ways with…
DECEMBER 9TH, 2024
Read More
Google Chrome Zero Day Vulnerability
IntroductionWe'd like to bring to your attention a high-severity vulnerability in Google Chrome browsers and Chromium-based browsers with active ongoing…
NOVEMBER 18TH, 2024
Read MoreNever miss a CIL Security Advisory
Stay informed with the latest security updates and insights from CIL.


